Are you looking for a way to track a phone secretly and for free? Free Secret Phone Tracker is a solution that helps you monitor a device’s location, activity, and status remotely at no cost. In this article, PhoneTracker247 will guide you on how to use free tracking tools safely, legally, and effectively, while also highlighting privacy risks you should avoid.
Contents
Key Features of Free Secret Phone Tracker
Free Secret Phone Tracker tools continue to evolve with smarter capabilities, helping users manage devices remotely with greater efficiency and control. Beyond basic tracking, these tools now focus on delivering a more comprehensive monitoring experience. However, to ensure safety and legality, users must always operate transparently and obtain proper consent from the device owner. Below are the enhanced key features and how they work in real-life scenarios.
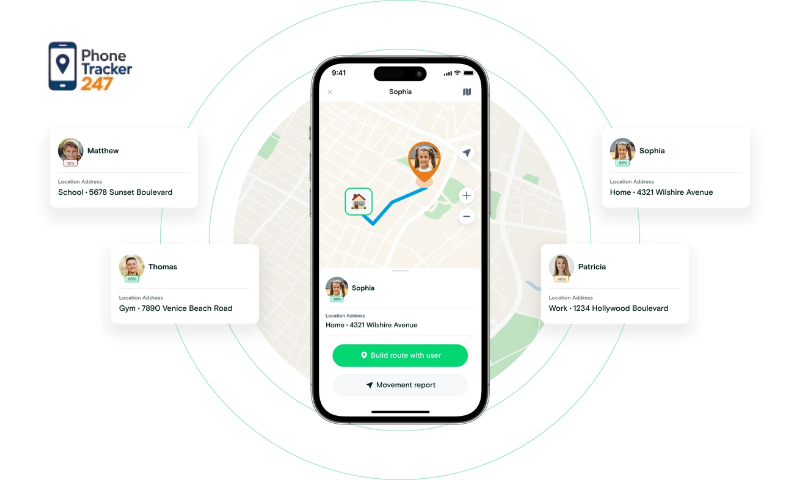
Real-Time GPS Location Tracking
- Determine a phone’s location via GPS, Wi-Fi, or mobile networks.
- Display real-time updates on an interactive map.
- Save detailed location history with timestamps for later review.
This feature is essential for keeping track of devices and ensuring the safety of loved ones, especially children or elderly family members. By analyzing movement history, users can better understand daily routines and identify unusual patterns. For optimal accuracy, combining GPS with Wi-Fi and network data is recommended, as environmental factors can sometimes affect precision.
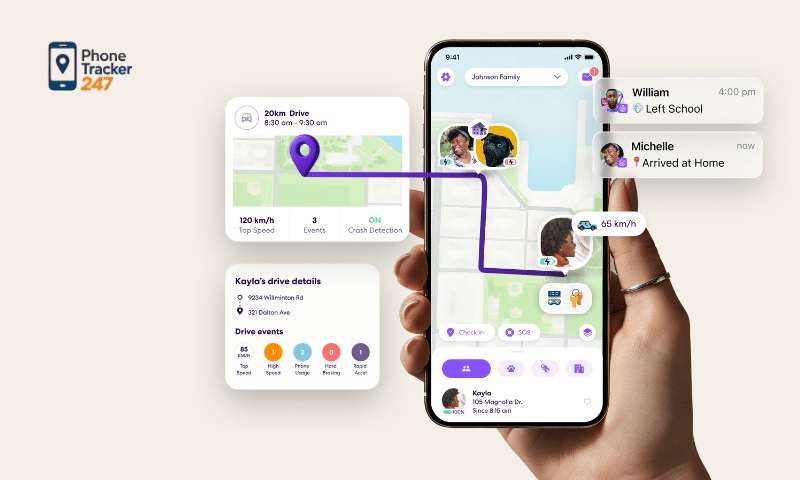
Device Activity Management
- Monitor screen time and frequently used applications.
- Analyze usage behavior across different time frames.
- Set geofencing zones and receive instant notifications when boundaries are crossed.
This feature provides deeper insight into how a device is being used, making it particularly valuable for parental control. Geofencing enhances safety by sending alerts when a device enters or exits predefined areas, such as schools or home zones. When applied responsibly, it helps users stay informed without being overly intrusive.
See more: Best Family Locator App Without Subscription: 2026 Safety Guide
Smart Alerts and Reports
- Send alerts when unusual activities are detected (e.g., sudden location changes or long-distance movement).
- Provide periodic summary reports on device location and activity.
- Present data in a clear, user-friendly format.
These capabilities act as a proactive monitoring system, allowing users to stay informed without constant supervision. Regular reports offer a comprehensive overview, helping identify usage patterns or unusual behaviors. This is particularly valuable for enhancing safety and minimizing risks, especially in emergency situations.
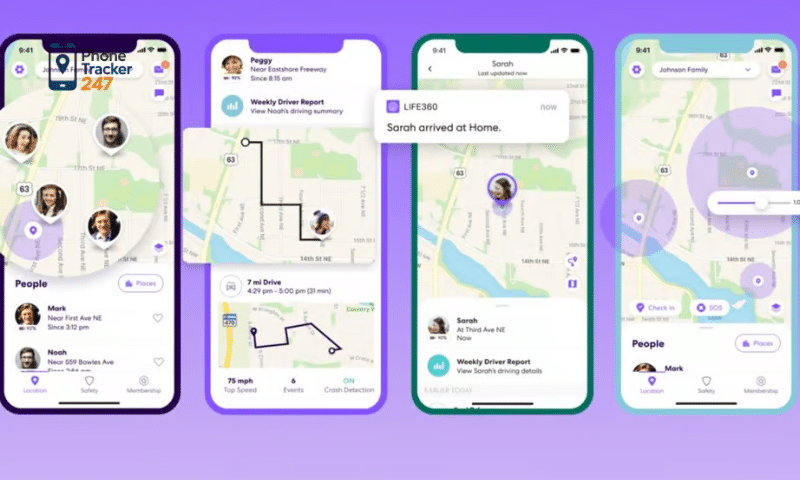
Overall Value and Benefits
Overall, Free Secret Phone Tracker tools go far beyond simple tracking—they offer a smarter, more proactive approach to device management and personal safety. When used correctly, they can:
- Strengthen device security and monitoring capabilities.
- Support effective family management and supervision.
- Identify risks early and respond to unusual situations quickly.
Ultimately, the key to maximizing these benefits lies in responsible use. Always respect privacy, communicate clearly, and comply with legal regulations to ensure these tools remain helpful rather than harmful.
How to Use Free Secret Phone Tracker Safely
Using Free Secret Phone Tracker tools goes beyond simple tracking—it requires a strong focus on safety, legality, and respect for privacy. When used incorrectly, these tools can expose users to data breaches or even legal consequences. Below is an expanded guide to help you use tracking tools responsibly and effectively.
Proper Installation and Setup
- Download apps only from trusted sources like Google Play Store or Apple App Store.
- Create a secure account and log in to manage your devices.
- Grant only essential permissions such as location, notifications, and network access.
Installing from official platforms reduces the risk of malware or fake apps that may compromise your data. It’s equally important to review each permission request carefully to avoid unnecessary access. A well-configured setup ensures better accuracy, smoother performance, and fewer technical issues over time.
Use Transparently and With Consent
- Track only devices you own or have clear permission to monitor.
- Communicate openly about the purpose of tracking (e.g., safety, parental control).
- Avoid any use that could infringe on personal privacy.
Although some tools are marketed as “secret,” using them without consent can violate privacy laws in many regions. Transparency builds trust and ensures compliance with regulations. When used ethically, tracking tools become a helpful solution rather than a potential legal risk.

See more: Tips to find my iPhone from my Android and locate the device easily
Protect Personal Data
- Keep your account credentials private and never share them with others.
- Use strong, unique passwords with a mix of characters.
- Enable two-factor authentication (2FA) for an added layer of security.
Tracking apps often handle highly sensitive data such as location history and user behavior. If this data is exposed, it can be misused or lead to security threats. Strengthening account protection is essential to safeguard both your information and the people being monitored.
Regular Monitoring and Updates
- Check app performance regularly to ensure accurate tracking.
- Install updates promptly to fix bugs and enhance security features.
- Reassess permissions and disable anything unnecessary.
Outdated applications may contain vulnerabilities that hackers can exploit. Regular maintenance helps keep the system secure and functioning correctly. This simple habit plays a major role in ensuring long-term reliability and safety.
Final Note on Responsible Usage
Ultimately, the effectiveness of Free Secret Phone Tracker tools depends on how responsibly they are used. Prioritize transparency, maintain strong security practices, and always follow legal guidelines. By doing so, you can fully benefit from these tools while protecting privacy and minimizing risks.

Conclusion
Free Secret Phone Tracker can be a useful solution for device management and family support when used properly. However, the most important factors remain respecting privacy and complying with the law.
If you are looking for a safe, transparent, and effective tracking solution, prioritize official and verified applications. At the same time, always use these tools for the right purposes to protect yourself and those around you.