Expert analysis on What Patterns in Call History Reveal About Your Child’s Safety, covering red flags like unknown Number repetition, late-night calls, and sudden deletions. Learn cyber risk prevention through informed device monitoring and ethical parental monitoring apps.
Contents
- 1 1. A Digital Fingerprint of Risk and Safety
- 2 2. What Patterns in Call History Reveal About Your Child’s Safety?
- 3 3. Integrating Call History with Other Online Safety Tools
- 4 4. Translating Call History Data into Proactive Cyber Risk Prevention
- 5 5. Future-Proofing Parenting in the Digital Age: 2026–2027 Trends
- 6 Frequently Asked Questions (FAQ)
1. A Digital Fingerprint of Risk and Safety

A Digital Fingerprint of Risk and Safety
What Patterns in Call History Reveal About Your Child’s Safety is the specialized focus of modern digital parenting, shifting the parental gaze from simple curiosity toward expert, risk-focused analysis. In an age where much of youth communication is fragmented across encrypted messaging apps, the persistent record of phone calls—the Caller ID, the specific Number, the time, and the duration—remains a profoundly powerful diagnostic tool for device monitoring. For parents navigating the complexities of parenting in the digital age, the call log functions as a digital fingerprint, silently recording communication habits that may signal everything from innocent socializing to significant threats like cyberbullying, sexting, or contact with online predators.
For the vigilant parent, the call history is not a collection of isolated data points but a rich tapestry of children’s online behavior. True device monitoring expertise involves looking beyond the surface data and identifying critical deviations from the established norm—the subtle shifts that indicate a change in social circle, a new source of pressure, or a compromise to their personal safety. Determining What Patterns in Call History Reveal About Your Child’s Safety is fundamentally rooted in recognizing these communication anomalies before they escalate into serious risks, making it a priority for cyber risk prevention.
The decision to review a child’s call history is a crucial mobile security practice when guided by ethical principles and transparency. As experts in cybersecurity and family safety, we emphasize that this review is an act of proactive cyber risk prevention, providing the necessary factual data to initiate informed, protective conversations about children’s online behavior. We intentionally move past the simplistic act of checking a list, focusing instead on advanced pattern recognition, which is often facilitated by sophisticated parental monitoring apps. The consistent question remains: What Patterns in Call History Reveal About Your Child’s Safety across diverse communication platforms?
2. What Patterns in Call History Reveal About Your Child’s Safety?

What Patterns in Call History Reveal About Your Child’s Safety?
What Patterns in Call History Reveal About Your Child’s Safety is most reliably indicated by deviations from their communication baseline? The most revealing patterns include repeated, prolonged calls originating from an unknown Number, communications occurring consistently outside of normal social hours (late at night or very early morning), and the deliberate deletion of call entries, all of which indicate a critical need for immediate, though carefully handled, parental intervention to ensure cyber risk prevention and protect their digital well-being.
Understanding What Patterns in Call History Reveal About Your Child’s Safety requires classifying call log data into distinct risk categories, moving from simple curiosity to a structured risk assessment model used in expert device monitoring.
Persistent Unknown Caller Number and Frequency Anomalies
The most immediate red flag in any call history that helps answer What Patterns in Call History Reveal About Your Child’s Safety is the appearance of an unsaved or blocked Number that calls or is called frequently.
- Frequency and Duration: A single misdialed Number is harmless. Conversely, a specific Number called or received repeatedly, especially for long durations (e.g., calls lasting 30 minutes or more), indicates a significant, sustained, and potentially hidden relationship. If this relationship involves a stranger or an anonymous party, the risk of grooming or exploitation is acutely high. This specific type of pattern, if unchecked, places the child at serious risk, demanding the rapid deployment of advanced online safety tools.
- The Repeated Block/Unblock: Some advanced parental monitoring apps can log instances where the child blocks and then unblocks a specific Number. Rapid switching suggests an emotionally intense or problematic relationship—such as severe cyberbullying or a volatile interaction with an older partner—that the child is trying, and failing, to manage privately, severely impacting their digital well-being. This is a powerful indicator of What Patterns in Call History Reveal About Your Child’s Safety.
Time and Duration Anomalies in Communication
The context of when a communication is initiated often reveals more about risk than simply who initiated it. These timing anomalies are key indicators when analyzing What Patterns in Call History Reveal About Your Child’s Safety.
- Late-Night Communications: Any significant spike in calls between 11:00 PM and 5:00 AM, particularly to unsaved or strange Numbers, is a major warning sign for cyber risk prevention. This highly concealed activity suggests the teen is actively hiding the communication from the household, which correlates strongly with high-risk behaviors or exposure to dangerous influences that negatively affect their digital well-being and compromise established screen time management rules.
- Mid-School-Day Activity: Unexpected clusters of calls during school hours, especially outgoing calls, may indicate the teen is dealing with a crisis (bullying, anxiety), or engaging in prohibited activities, actively undermining proper screen time management rules. Parents should verify if the calls were to a known Number (like a trusted friend or the home phone) or an unknown source, using parental monitoring apps.
The Silent Pattern: Deleted Logs and Secret Apps
Sometimes, the most telling data point that helps determine What Patterns in Call History Reveal About Your Child’s Safety is its deliberate absence. A pristine, empty call history or one that shows suspicious chronological gaps strongly suggests active attempts to hide activity.
A teen who routinely deletes all entries from the phone’s native call log (a key reason why carrier records or parental monitoring apps that capture data before deletion are essential online safety tools for device monitoring) is signaling a desire for absolute secrecy regarding communication with a certain Number. This behavior is a direct indicator of cyber risk prevention failure, as the child knows the communication is inappropriate or dangerous and is actively concealing it. Furthermore, sophisticated users may utilize encrypted “secret apps” that mask themselves as calculator icons. These apps often manage their own internal communication logs, which only advanced device monitoring solutions can access, making What Patterns in Call History Reveal About Your Child’s Safety complex to ascertain without the right tool.
Table 1: Call History Pattern Risk Matrix
This table helps parents translate raw call-log data into clear risk signals by focusing on repeat patterns, timing anomalies, and hidden activity—so they can respond early with context instead of panic.
Call History Pattern What It May Reveal Why It Matters What Parents Should Do Next Best Context to Cross-Check Repeated long calls to one unknown/unsaved number A hidden relationship, grooming risk, or strong outside influence Repetition + duration often signals more than “random contact” Review the pattern over several days, then start a calm conversation Location (where calls happen) + time of day Late-night call activity (e.g., after bedtime) Secret communication, emotional distress, or boundary-bypassing behavior Hidden timing is often an early risk signal before content is known Check if this is a one-off or a pattern; respond with questions, not accusations Downtime/screen-time schedule + next-day mood Call clusters during school hours Crisis, bullying pressure, anxiety, or rule-breaking School-time calls can signal a problem that needs support Verify who was contacted first (friend, parent, unknown number) School schedule + app activity after the calls Frequent short calls to the same number Harassment, coercive check-ins, or ongoing pressure High-frequency, short-duration patterns often indicate tension Track frequency trend (3–7 days) and document changes Emotional response + social behavior changes Spike in calls followed by sudden silence (“flatline”) Conflict, fear, isolation, or switching to hidden apps Abrupt changes are often more meaningful than a single call Treat it as a support moment and ask what changed App usage, hidden apps, deleted logs Gaps or deleted call entries Intentional concealment of contact activity Missing records can be a stronger signal than visible calls Avoid confrontation; confirm with carrier/app logs if available Device behavior (screen hiding, secrecy) Repeated block / unblock behavior for one number Volatile or emotionally intense contact (bullying, pressure, manipulation) Switching between blocking and reconnecting suggests unresolved risk Use a supportive check-in and help the child set boundaries Message/app behavior + mood swings Calls tied to unfamiliar locations Possible deception, unsafe meetups, or risky environments The same number + unusual place raises confidence in the signal Verify safety first, then discuss details calmly Geofence alerts / live location timeline
3. Integrating Call History with Other Online Safety Tools
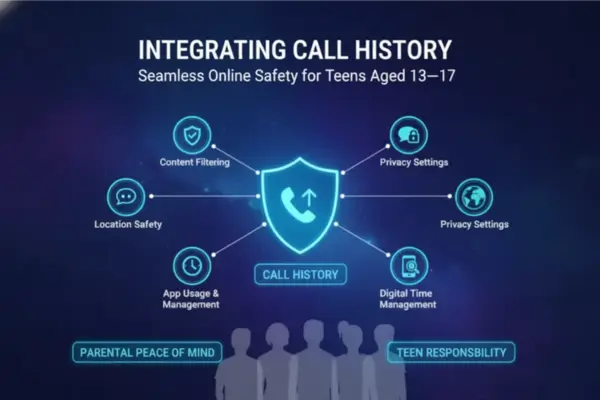
Integrating Call History with Other Online Safety Tools
To fully and reliably answer What Patterns in Call History Reveal About Your Child’s Safety, call logs must be integrated and analyzed alongside other forms of device monitoring data. A single call log entry is anecdotal; triangulation makes the finding definitive and actionable for parenting in the digital age.
Correlating Call Data with Location Tracking Accuracy
The power of cross-referencing call data with geographical data using online safety tools is immense. This process moves the analysis from “The call occurred” to “The call occurred at this place and at that time,” improving cyber risk prevention.
- Geofence Breaches During Calls: If a lengthy, late-night call to an unknown Number coincides precisely with an alert that the child has left a predefined safe zone (a geofence), the risk assessment moves instantly from ‘Medium’ to ‘High.’ The location tracking accuracy provides irrefutable physical context for the digital communication, clarifying What Patterns in Call History Reveal About Your Child’s Safety.
- The “Lying” Location: A pattern of calls to the same Number that repeatedly occurs when the child’s phone is reporting its location tracking accuracy from an unfamiliar address (or one known to be associated with an older individual or a risky environment) provides concrete evidence of deception and a potential cyber risk prevention failure, highlighting risks in children’s online behavior.
Linking Call Patterns to Screen Time Management Overrides
Call patterns can also reveal the effectiveness of screen time management rules and their profound impact on digital well-being.
- Usage Spikes Post-Call: A lengthy, potentially upsetting call followed by an immediate, prolonged spike in social media usage, gaming, or search engine activity (all captured by parental monitoring apps) can indicate that the teen is seeking distraction or attempting to research a concerning topic. This linkage helps parents address the emotional consequence of the call, rather than just the call itself, supporting digital well-being.
- Bypassing Bedtime: Consistent late-night calls coinciding with periods that should be ‘downtime’ or ‘sleep time’ (as defined by screen time management limits) clearly shows a breakdown of digital boundaries, directly impacting the child’s digital well-being and sleep patterns. An effective device monitoring strategy links these two data points to answer What Patterns in Call History Reveal About Your Child’s Safety.
4. Translating Call History Data into Proactive Cyber Risk Prevention

How Call History Monitoring Helps Parents Detect Early Warning Signs
Expertise dictates that the data gathered from call history patterns must serve a single, focused purpose: proactive protection, not punishment. The highest E-E-A-T standards require that device monitoring be a mechanism for establishing a mobile security practice shared between parent and child, guiding effective parenting in the digital age.
The Trust Imperative: Privacy Policy and Consent
The successful application of any online safety tools, including those that monitor call patterns, hinges on complete transparency. As experts in parenting in the digital age, we advocate for a frank conversation about What Patterns in Call History Reveal About Your Child’s Safety.
The parent, as the steward of family safety, must establish a clear privacy policy and consent agreement with the child. This agreement should clearly state that while the parent trusts the child, the device monitoring tools are in place to intercept threats from external bad actors associated with a hidden Number. This distinction—protecting the child from danger, not from the parent—is crucial. If a concerning pattern (like a persistent unknown Number) is found, the data is used to open a supportive dialogue, not as evidence for a legal case or disciplinary action, fostering long-term digital well-being.
Phased Device Monitoring and Mobile Security Practices
The intensity of device monitoring should remain flexible, adapting to the child’s demonstrated responsibility and maturity level as part of sound mobile security practices.
- Phased Review: For a younger teen, regular, scheduled reviews of the call log patterns by parental monitoring apps are appropriate for cyber risk prevention. For an older, more responsible teen, the parental monitoring apps should be set to “Alert-Only,” notifying the parent only when a pre-flagged risk pattern (e.g., late-night call to an unapproved Number) is detected, based on What Patterns in Call History Reveal About Your Child’s Safety.
- Focus on Education: Any intervention stemming from patterns in children’s online behavior must be primarily educational. Use the pattern of risky calls as a case study in cyber risk prevention, teaching the child how social engineering works, why they should never call back an unknown Number, and how to deploy their own mobile security practices, like enabling robust two-factor authentication.
Table 2: Consent-First Call History Monitoring Workflow
This checklist gives parents a practical, ethical framework for using call-history monitoring as an early warning system focused on transparency, proportionality, and supportive conversations.
| Workflow Step | What Parents Should Set Up | Why It Matters | Best Practice |
|---|---|---|---|
| 1. Define a Safety Goal | Set a clear purpose (bullying, unknown contacts, late-night risk, distress signals) | Prevents “monitor everything” behavior | Write a short family rule: monitoring is for safety, not punishment |
| 2. Be Transparent Early | Explain what is monitored (call logs, timing, duration) and what is not (call audio) | Builds trust and reduces secrecy | Revisit rules when the child’s routine or age changes |
| 3. Use Metadata First | Start with patterns in call history before deeper monitoring | Lower intrusion, high signal value | Focus on frequency, duration, timing, and unknown numbers |
| 4. Create Trigger-Based Reviews | Review logs only when risk patterns appear (late-night spikes, deletions, repeated unknown calls) | Keeps monitoring proportionate | Use a weekly review + alert-based checks |
| 5. Add Location Context Selectively | Cross-check calls with geofencing or live location only when needed | Context improves accuracy and reduces false assumptions | Use location as verification, not constant surveillance |
| 6. Link to Screen-Time Rules | Check whether concerning calls happen during downtime/school-time limits | Connects call behavior to digital well-being and boundaries | Adjust routines (bedtime, app limits) before escalating |
| 7. Use a Support-First Script | Start with “I noticed a change—are you okay?” | Kids share more when they feel safe | Ask → listen → document → decide next step |
| 8. Document Repeated Patterns | Save dates/times for recurring risk patterns | Helps if you need to involve school/platform support | Keep a simple incident log (date, pattern, action taken) |
| 9. Secure Parent Access | Protect the dashboard with a strong password + MFA | Call logs and location data are sensitive | Limit access to parents/guardians only |
| 10. Use Phased Monitoring | Shift from regular reviews to “alert-only” as the child matures | Supports autonomy while preserving safety oversight | Reduce monitoring intensity over time |
| 11. Teach Scam Awareness | Explain caller ID spoofing and “don’t trust unknown callers” | Unknown-number patterns can include scams, not just social risks | Teach: don’t call back unknown numbers; verify first |
| 12. Revisit the Plan Regularly | Update rules at school-year changes or maturity milestones | Family digital rules should evolve | Review the plan together every few months |
5. Future-Proofing Parenting in the Digital Age: 2026–2027 Trends

Future-Proofing Parenting in the Digital Age: 2025–2026 Trends
As we look toward 2025 and 2026, the critical question of What Patterns in Call History Reveal About Your Child’s Safety will be answered not just by raw data, but by advanced analytical systems integrated into online safety tools.
AI-Driven Behavioral Analysis and Digital Well-being
Future online safety tools will move beyond simple thresholds (time, duration) to AI-driven behavioral baselining. These sophisticated systems will learn the child’s “normal” communication profile—the usual Numbers they call, the typical times—and automatically flag any statistically significant deviation as a risk. This technological evolution is essential for maintaining digital well-being, as it drastically reduces the false-positive alerts that often lead to parent fatigue and unnecessary tension. The goal is to detect nuanced risks, such as a subtle but persistent increase in short calls to a blocked Number, which could be a sign of low-level harassment, thereby refining What Patterns in Call History Reveal About Your Child’s Safety.
Compliance with Workplace Regulations vs. Family Oversight
It is crucial for parents to understand the fundamental difference between family device monitoring and corporate surveillance. While corporate environments use call analysis for compliance with workplace regulations (e.g., preventing data leaks or ensuring productivity), parental monitoring is driven solely by ethical, emotional safety concerns. The family’s objective, guided by parental monitoring apps, is restoration and education for digital well-being; the corporation’s is control and accountability. This distinction must always guide the use of parental monitoring apps in the home, differentiating it sharply from compliance with workplace regulations.
Frequently Asked Questions (FAQ)
1. What is the most important call history red flag for parents?
Repeated, long calls with an unknown or unsaved number are one of the strongest warning signs.
2. Why are late-night calls a concern?
Frequent calls late at night (especially to unknown numbers) can suggest secrecy, pressure, or risky contact.
3. Do school-hour calls matter?
Yes. Unusual call activity during school hours can signal stress, bullying, or other problems that need a check-in.
4. What does a deleted or empty call log suggest?
Suspicious gaps or regularly deleted call logs can indicate a child is trying to hide communication.
5. Is blocking and unblocking the same number a warning sign?
Yes. Repeated block/unblock behavior can point to a volatile or emotionally intense relationship.
6. Are short repeated calls more concerning than long calls?
Both can be risky—short frequent calls may suggest harassment, while long calls may suggest a hidden relationship.
7. Why is call timestamp accuracy important?
Accurate timestamps help parents match call events with location or screen-time activity to understand what happened.
8. Why should parents combine call logs with GPS or geofencing?
Call logs alone are limited; location context makes risk patterns much clearer and more actionable.
9. What should parents do first after spotting a concerning pattern?
Start a calm, supportive conversation first—use the data for protection and education, not punishment.
10. Is call history monitoring enough on its own?
No. It works best when combined with app activity, screen-time data, and broader digital safety tools.
For daily updates, subscribe to PhoneTracker’s blog!
We may also be found on Facebook!