Discover the expert methods for how to find incognito history on android devices. This 2026 guide covers forensic techniques, specialized parental monitoring app 2026, and ethical digital parenting for absolute cyber-safety.
Contents
- 1 1. The Illusion of Anonymity: Why Incognito Mode is Not a Shield
- 2 2. The Technical Divide: Why Android Doesn’t Save Private History
- 3 3. Expert Methodologies: How to Find Incognito Browsing History on Android with Precision
- 4 4. The Ethical Mandate: Transparency in Device Monitoring and Privacy Policy and Consent
- 5 5. Data Integration: Turning Incognito Traces into a Cyber-Risk Prevention Strategy
- 6 FAQs: Expert Answers on Tracing Private Android Activity
1. The Illusion of Anonymity: Why Incognito Mode is Not a Shield
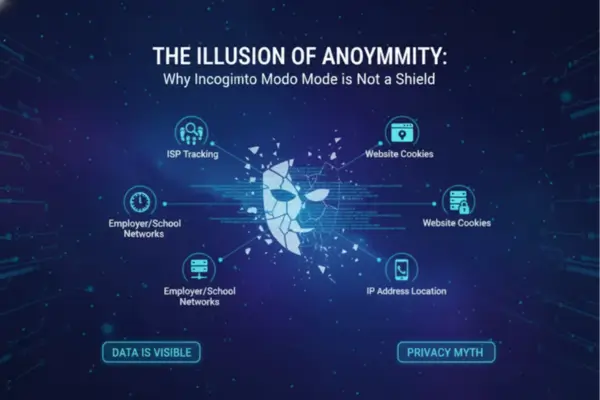
The Illusion of Anonymity: Why Incognito Mode is Not a Shield
Incognito Mode on Android, while effective at hiding activity from other local device users, is merely an illusion of complete anonymity. It works by preventing the saving of browsing data, cookies, and search history to the device’s local filesystem; however, it does not hide activity from the network administrator, the Internet Service Provider (ISP), or specialized system-level parental monitoring apps, all of which retain persistent logs and metadata crucial for effective cyber-risk prevention
The rise of the smartphone has brought with it an almost instantaneous access to information, yet it has also introduced unparalleled challenges to parenting in the digital age. Many teenagers, believing they are deleting their digital footprint, turn to Chrome’s Incognito or other private browsing modes on their Android devices. The misconception is pervasive: if the history isn’t visible, it must be gone. This is where the crucial work of modern device monitoring begins, moving past marketing claims to forensic reality.
Incognito Mode is specifically designed to be volatile—meaning the session data is stored in the device’s volatile memory (RAM) and wiped clean upon closing the tab. This makes it a formidable obstacle to conventional checks. However, a shadow of the activity always remains. When addressing the challenge of how to find incognito history on android, experts understand that the search must shift from the browser interface itself to the network layer and the operating system’s deeper data streams. These residual traces are the keys to maintaining online safety tools that actually work in today’s environment.
2. The Technical Divide: Why Android Doesn’t Save Private History

The Technical Divide: Why Android Doesn’t Save Private History (and Where the Traces Go)
Mastering Techniques: How to Find Incognito History on Android
Android’s Chrome browser is engineered not to store incognito history in the standard database files. Therefore, parents cannot find it using typical methods. However, traces are recoverable because the device’s Domain Name System (DNS) cache logs the domain name lookups for a temporary period, and the Internet Service Provider (ISP) or Wi-Fi router retains full network traffic logs, providing a definitive answer to the user’s online whereabouts.
The Volatility of RAM and Browser Cache
When a child initiates an Incognito session on an Android phone, the browser creates a temporary, isolated environment. Any information—cookies, site data, and browsing history—is written to the device’s Random Access Memory (RAM). RAM, by its nature, is volatile; once the Incognito tab is closed, or the phone is rebooted, this data is lost. This is the primary mechanism that frustrates parents attempting to manually check the history.
This inherent volatility highlights the limitations of standard mobile security practices. Without a specialized tool capable of logging data as it occurs (in real-time) or conducting a full forensic analysis of the RAM image (a technique far beyond the average user), the data appears irrecoverable. This is the technical challenge that necessitates professional solutions when attempting to determine how to find incognito browsing history on Android.
The Persistent Record: DNS Cache and Network Logs
While the Android browser may be silent, the network infrastructure is not. Every time a device visits a website, it must communicate with the Domain Name System (DNS) to translate the website’s name (e.g., https://www.google.com/search?q=Google.com) into an IP address.
- Local DNS Cache: The Android OS maintains a local DNS cache to speed up subsequent visits. Even an Incognito session often leaves domain names—though not the full, specific URLs—in this cache temporarily. While this cache can be manually cleared (e.g., via
chrome://net-internals/#dns), it is a persistent, if fleeting, artifact. - External Network Logs: More significantly, the Wi-Fi router or the ISP logs every IP address connection. This logging happens entirely outside the phone’s control. A network administrator (or a parent with administrative access to their home router) can retrieve logs that show the domain names visited. This forms an indisputable, permanent record, regardless of the child’s attempt to erase history on their Android device.
Table 1: Incognito on Android, What Disappears vs What Still Leaves Traces
This table helps parents understand what Incognito mode removes from the phone itself, what may still be visible through network or monitoring layers, and which options are safer for ongoing child-safety monitoring.
| Layer / Signal | What Incognito Hides | What May Still Be Visible | Main Limitation | Best Parent Use |
|---|---|---|---|---|
| Chrome local history (on-device) | Browsing history and site data are not kept after the Incognito session ends | Little to no usable local browsing history after tabs are closed | Parents usually cannot “recover” closed Incognito history from Chrome directly | Use this only to confirm current behavior, not past private sessions |
| Chrome session artifacts (during active session) | Incognito separates activity from normal browsing | Temporary session data exists only while the private session is open | Once all Incognito windows close, local session traces are removed | Focus on prevention and live alerts, not late manual checks |
| Downloads & bookmarks | Incognito hides browsing history | Files downloaded and bookmarks saved still remain on the device | These don’t show full browsing context by themselves | Spot-check risky downloads or suspicious bookmarks |
| Network-level visibility (home Wi-Fi / ISP / school network) | Incognito does not hide activity from the browser’s local history only | Network operators may still observe traffic/activity | Requires router/admin access or provider-level logs | Useful for household-level verification and web filtering strategy |
| Family Link (supervised child account in Chrome) | Child cannot use Incognito in Chrome when supervised | Parents can apply website filters, block/allow lists, and approve requests | Works best in supervised Chrome; browser/app coverage is not universal | Baseline protection for younger kids/teens using Chrome |
| System-level parental monitoring app | Incognito hides browser history, not always system-level observations | URL patterns, activity signals, or alerts may be captured in real time (depending on permissions/features) | Requires correct setup, permissions, and a transparent family policy | Best for ongoing risk detection (unsafe sites, evasion patterns) |
| Parent review workflow (rules + alerts) | Incognito can hide visible history from quick manual checks | Behavior patterns still show up (late-night browsing, repeat risky domains, evasive behavior) | Monitoring without communication can damage trust | Use alerts to start calm conversations, not punishments |
3. Expert Methodologies: How to Find Incognito Browsing History on Android with Precision

Expert Methodologies: How to Find Incognito Browsing History on Android with Precision
The Technical Divide: Why Android Doesn’t Save Private History (and Where the Traces Go)
The most reliable way to find incognito browsing history on Android is to deploy a system-level parental monitoring app that utilizes Accessibility Services and keylogging to capture the URL in real-time before the browser can isolate the private session. These tools bypass the browser’s memory management by recording the input and output at the operating system layer, providing continuous, secure data capture.
Utilizing System-Level Parental Monitoring Apps
For parents seeking clarity and control in digital parenting, high-quality parental monitoring apps represent the most practical solution. These are not simple web filters; they are sophisticated online safety tools operating with elevated system privileges.
- Real-Time Data Capture: The best applications for how to find incognito browsing history on Android employ sophisticated techniques like accessibility monitoring, which can read the URL bar content as it changes, even in an Incognito tab. This data is instantly encrypted and uploaded to the parent’s secure dashboard, creating an independent log that the child cannot delete.
- Keystroke Logging Integration: By logging keystrokes, these tools capture search queries and full URLs as they are typed, providing irrefutable evidence of the child’s intent and activity, regardless of whether the site successfully loads or is instantly closed.
This method transforms the opaque world of private browsing into clear, actionable data, which is essential for effective cyber-risk prevention.
Deep-Dive Forensic Techniques: Analyzing Artifacts
While requiring specialized technical knowledge, forensic analysis confirms that even in Incognito, artifacts remain. Digital forensic experts use techniques to retrieve data that the average parent cannot:
- RAM Acquisition: During an active Incognito session, data is stored in RAM. Forensic analysts can perform a ‘memory dump’ to capture the contents of the RAM, which can then be analyzed for remnants of browser history, search terms, and even login credentials.
- SQLite Database Recovery: Even if the main history file is cleared, fragments of data can persist in the app’s ancillary files, metadata, or unallocated space on the flash memory. Specialized software can piece these fragments together to reconstruct parts of the browsing timeline.
These forensic methodologies underscore a fundamental truth: digital information is highly persistent. The question is never if the history can be found, but rather how to find incognito browsing history on Android using the right combination of tools and expertise.
4. The Ethical Mandate: Transparency in Device Monitoring and Privacy Policy and Consent

The Ethical Mandate: Transparency in Device Monitoring and Privacy Policy and Consent
Effective and ethical device monitoring hinges on transparency, particularly when utilizing sophisticated tools to uncover sensitive activities like incognito browsing. Responsible digital parenting demands that a clear privacy policy and consent framework be established, converting covert surveillance into mutually agreed-upon oversight focused on cyber-risk prevention, thereby strengthening, rather than shattering, family trust.
Drawing the Line Between Oversight and Surveillance
The act of monitoring a child’s digital life, especially their private browsing, must be framed by mutual respect. When parents move to actively address how to find incognito browsing history on Android, they must be mindful of the ethical implications. The objective is not punitive control but proactive protection.
True ethical device monitoring recognizes that a child’s digital well-being is inextricably linked to their sense of autonomy. Unannounced monitoring often leads to broken trust, prompting children to adopt more extreme measures to hide their children’s online behavior. The aim is always to educate and empower, not to catch and punish.
The Digital Well-Being Agreement: A New Standard for Parenting in the Digital Age
The solution lies in formalizing expectations through a “Family Digital Agreement.” This is a documented understanding of the rules of engagement that clearly defines the boundaries of privacy policy and consent.
The agreement should explicitly state:
- What is Monitored: Clearly outline that all activity, including private browsing, is visible via the parental monitoring apps.
- Why: State the purpose is for safety (e.g., detecting cyberbullying, grooming, or self-harm content), not for reading private messages or academic oversight.
- Limits: Define when the monitoring will be reduced or phased out (e.g., based on age or demonstrated digital maturity).
This proactive approach not only adheres to modern privacy policy and consent standards but also transforms monitoring into a teaching moment, promoting healthier children’s online behavior from the outset.
Table 2: Consent-First Workflow for Handling Incognito Browsing Risk on Android
This checklist gives parents a practical, ethical way to manage Incognito-related risk by combining Chrome controls, supervised accounts, alerts, and transparent family rules instead of “catching” kids after the fact.
| Step | What Parents Should Do | Why It Matters | Best Practice |
|---|---|---|---|
| 1. Start with a Safety Goal | Define the purpose (unsafe websites, grooming risk, explicit content, scam links) | Prevents “monitor everything” behavior | Write a short family rule: monitoring is for safety, not punishment |
| 2. Explain Incognito Clearly | Tell your child that Incognito hides local history, not all online activity | Corrects the “invisible online” myth early | Use a calm, educational explanation instead of fear |
| 3. Use Family Link as the Baseline | Set up supervised Chrome controls (filters, site approval, block/allow lists) | It reduces risk before deeper monitoring is needed | Start with “Try to block explicit sites” + approved/blocked sites |
| 4. Know the Coverage Limits | Assume Chrome controls are strong but not universal across every app/browser | Kids may switch tools or channels when rules tighten | Combine Chrome controls with broader device-level safety routines |
| 5. Use Trigger-Based Monitoring | Review activity only when risk signals appear (unsafe searches, late-night spikes, repeated evasion) | Keeps monitoring proportional and more ethical | Use alerts and patterns, not constant thread-by-thread checking |
| 6. Prioritize Prevention Over Recovery | Focus on blocking/filtering and real-time alerts instead of trying to “recover” closed Incognito history | Closed Incognito sessions are designed to leave minimal local traces | Build a forward-looking safety system |
| 7. Add Screen-Time & Routine Controls | Use bedtime limits, study-time rules, and app restrictions | Reduces risk exposure windows, especially late at night | Pair content controls with time controls |
| 8. Use a Calm Response Script | Start with: “I noticed a pattern—are you okay?” | Kids disclose more when they don’t fear immediate punishment | Ask → listen → support → adjust rules |
| 9. Keep Data Minimal and Secure | Retain only useful logs/alerts and secure parent access | Monitoring data is sensitive family data | Use strong passwords and a short retention window |
| 10. Review and Reduce Over Time | Reassess monitoring depth as your child matures | Supports autonomy and long-term trust | Move from full reviews → alert-based oversight |
5. Data Integration: Turning Incognito Traces into a Cyber-Risk Prevention Strategy

Data Integration: Turning Incognito Traces into a Cyber-Risk Prevention Strategy
The trace of incognito browsing is a vital clue, but its full value is unlocked only when integrated into a comprehensive strategy. Effective cyber-risk prevention involves cross-referencing these traces with location tracking accuracy data, app usage patterns, and screen time management reports to create a holistic risk profile, enabling parents to see high-risk patterns instead of isolated events.
A successful modern mobile security practices protocol relies on synthesis. An isolated DNS entry from an Incognito session is ambiguous. However, if that entry coincides with:
- A sudden change in location tracking accuracy (e.g., the child unexpectedly deviates from their routine route home).
- A frantic period of deleting apps immediately following the browsing session.
- An unusual spike in usage time for an unfamiliar messaging app, revealed by screen time management logs.
.This integration allows parents to move from mere reaction to proactive cyber-risk prevention. The focus shifts from “What site did they visit?” to “What is the collective risk level of their current digital actions?” This is the core philosophy that drives platforms like PhoneTracker247, which provides the integrated online safety tools necessary to connect these disparate data points.
FAQs: Expert Answers on Tracing Private Android Activity
1. What does Incognito mode hide on Android?
Incognito mainly hides local browser history, cookies, and site data from other users on the same device after the session ends.
2. Does Incognito mode make a child invisible online?
No. The article explains activity may still be visible through network logs or system-level monitoring tools.
3. Why can’t parents see Incognito history in Chrome normally?
Chrome on Android is designed not to store Incognito history in the standard browser history database.
4. Can DNS cache reveal Incognito browsing?
Sometimes. DNS cache may temporarily show visited domains, but it is short-lived and easy to clear.
5. Are router or ISP logs more reliable than phone history?
Yes. The article says network logs can provide a more persistent record than the phone’s local browser data.
6. What is the most practical way for parents to monitor Incognito use?
The guide recommends a system-level parental monitoring app that logs activity in real time.
7. Can monitoring tools detect Incognito activity without rooting Android?
Yes. The article says modern tools can use Android accessibility features instead of rooting.
8. Can a VPN fully hide Incognito activity from parental monitoring apps?
Not always. The article says device-level monitoring can capture activity before VPN encryption is applied.
9. Is Google Family Link enough to see exact Incognito URLs?
Usually no. The article says Family Link is useful for controls, but not for detailed Incognito URL tracking.
10. What is the ethical way to monitor Incognito browsing?
Use a clear family agreement, explain what is monitored, and focus on safety rather than punishment.
For daily updates, subscribe to PhoneTracker’s blog!
We may also be found on Facebook!